Tom Scott is shocked [Bad way of putting it, sorry, see the comments] that OAuth granted permission to applications to read user's direct messages. That's obvious to me as a developer. Everything else a non-private user does on the service is freely available through the search API and streams so there's no need to ask for permission. The important point is that Tom's confusion shows how little even sophisticated users understand Twitter's comparatively simple security model. What made my heart sink was his suggestion that Twitter go down the Facebook path and offer more fine-grained permissions.
If users don't have the time to understand the current model, does he really think they'll spend time tweaking a set of checkboxes? When Internet Explorer throws up dialogs complaining about a mix of secure and unsecure content on a page, does any user know what that means? The Facebook/Microsoft approach is a bunch of legalistic ass-covering by people keen to avoid blame, not a good way of getting informed consent from users.
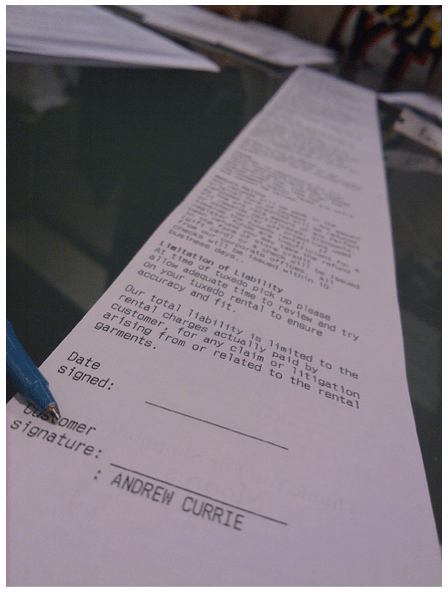
Just look at this exhaustive study of the effect of contract disclosures on internet user's habits. Hardly anybody reads them, and the few who do don't change their behavior at all! The prevailing model of user security permissions hits exactly the same problem. We've trained our users to click through screens of goobledegook without reading or caring.
So what's the answer? No checkboxes. No space-shuttle control panel of permissions. The only model that people understand is completely binary, public or private, open or closed. Look back to the phone book, everyone understood going ex-directory, and that's all you needed to know. In Twitter's case, this means redesigning the OAuth process so that it's just a 'give me access to your DMs' dialog, since for almost all users that's what it really means. It's not a technology problem, it's a user-experience one.